Security and artificial intelligence have become inseparable in 2026 — not because the industry made a deliberate decision, but because the threat landscape forced it. The same large language models that compress a phishing campaign from 16 hours of work into 5 minutes for an attacker are also the engines powering next-generation security operations centers that cut breach response times by 80 days. AI-in-cybersecurity is a dual-use technology problem: every advancement in defensive AI capabilities is simultaneously an advancement in offensive capabilities for threat actors who access the same underlying models. The IBM 2025 Cost of a Data Breach report provides the clearest quantification of where the defensive advantage currently sits — organizations making extensive use of AI and automation in security paid an average of $3.62 million per breach versus $5.52 million for organizations with no AI/automation, a 34% cost reduction driven by faster detection, faster investigation, and faster containment.
- AI-in-cybersecurity market: $29.64–$35.91 billion in 2025, projected to reach $86.34 billion by 2030 at 22.8% CAGR (Mordor Intelligence) — the fastest-growing segment in cybersecurity.
- IBM 2025: organizations with extensive AI/automation in security pay $3.62M per breach vs. $5.52M without AI — a 34% cost reduction; breach identification + containment lifecycle shortened by 80 days (264 → 184 days).
- 61% of cybersecurity teams adopted AI-powered threat detection in 2025; 88% of security professionals say AI tools are critical to SOC efficiency (Darktrace).
- AI-generated phishing surged 1,265% since 2023; 82.6% of phishing emails in 2025 used AI assistance; AI phishing click-through rates reach 54% vs. 12% for human-crafted lures.
- 80% of ransomware attacks in 2025 leveraged AI tools (MIT study); deepfake incidents increased tenfold globally with +1,740% growth in North America.
How AI Strengthens Cybersecurity Defense
The defensive application of AI in cybersecurity has moved beyond marketing language into measurable operational outcomes. Detection models trained on billions of security events identify behavioral anomalies that rule-based systems miss; LLMs integrated into investigation workflows compress triage timelines; agentic AI systems execute remediation actions autonomously when analysts are unavailable or overwhelmed. The 2025 data shows the cumulative effect: the global mean time to identify and contain a breach reached 241 days — the lowest in nine years — with AI-equipped organizations achieving 184 days versus 264 days for organizations without AI, an 80-day improvement that directly translates to reduced attacker dwell time and lower breach costs.
AI-Powered Threat Detection: CrowdStrike, Microsoft, and Darktrace
CrowdStrike’s Charlotte AI, embedded in the Falcon platform, reports 98% decision accuracy and saves analysts approximately 40 hours per week in investigation time. The Fall 2025 CrowdStrike release introduced Charlotte AI AgentWorks — a no-code agent builder allowing analysts to create autonomous SOC workflows in plain language, executing multi-step investigation and response sequences without custom scripting. Microsoft Security Copilot became available to all Microsoft 365 E5 customers in November 2025 (400 Security Compute Units per 1,000 user licenses); its Phishing Triage Agent identifies malicious emails 6.5x faster than manual review and improves verdict accuracy by 77%. Palo Alto Networks’ Cortex AgentiX, launched in October 2025, was trained on 1.2 billion real-world playbook executions — bringing operational institutional memory into automated response at a scale no human analyst team could match.
Darktrace’s Cyber AI Analyst operates differently: rather than augmenting human analysts, it acts as an autonomous parallel team. Darktrace reports the platform provides the equivalent of 30 additional SOC analysts, with its Autonomous Response capability containing threats surgically in real time without disrupting business operations. In Darktrace’s 2025 State of AI Cybersecurity report, 88% of security professionals said AI tools are critical to improving SOC efficiency — a figure that reflects how thoroughly AI has embedded into security operations expectations. The underlying techniques driving these platforms — user and entity behavior analytics (UEBA), ML-based anomaly detection, LLM-assisted alert triage — reduce analyst false-positive alert volume by up to 95% compared to signature-only detection, which is the primary productivity driver cited for AI adoption in modern SOC environments. Security analytics platforms increasingly treat agentic AI as a core architectural component rather than an add-on feature.
The ROI of AI Security: Breach Cost and Response Time Data
The IBM 2025 Cost of a Data Breach report provides the most widely cited quantification of AI security ROI. Organizations with extensive AI and automation across their security operations paid an average breach cost of $3.62 million versus $5.52 million for organizations without AI — a $1.9 million differential. Beyond the headline cost figure, the IBM data breaks down specific AI capabilities by their per-breach cost contribution: AI and ML security insights contribute an average savings of $223,503 per breach; security analytics and SIEM platforms contribute $212,061; DevSecOps approaches contribute $227,192. The compound effect of deploying multiple AI-enabled security capabilities simultaneously accounts for the full $1.9 million differential across organizations with mature AI security programs versus those still operating primarily on rule-based detection.
The response time data is equally significant from a risk management perspective. The 80-day difference in breach identification and containment between AI-equipped and non-AI organizations represents 80 days of attacker dwell time — the period during which adversaries can exfiltrate data, establish persistence, move laterally, and deploy ransomware. Every day of dwell time adds to breach cost: at IBM’s documented breach cost rates, 80 days of additional dwell time in a large enterprise environment translates to breach cost impact well beyond the $1.9 million headline differential for organizations at the high end of the data volume and regulatory exposure spectrum. Threat intelligence integration with AI-powered detection platforms is documented as one of the strongest multipliers of the response time improvement — intelligence-enriched AI detection systems identify active attacks significantly faster than AI detection alone.
AI Cybersecurity Market Growth and Adoption
The AI-in-cybersecurity market was valued at $29.64–$35.91 billion in 2025, with projections ranging from $86.34 billion by 2030 (Mordor Intelligence, 22.8% CAGR) to $167.77 billion by 2035 (Precedence Research). In 2025, 144 AI security deals closed — the highest of any cybersecurity category in a single year, reflecting institutional capital consolidating around AI-native vendors as the strategic infrastructure layer for security operations. 61% of cybersecurity teams adopted AI-powered threat detection tools in 2025 — yet 29% of those organizations still suffered AI-based breaches in the same year, which underlines a critical nuance: AI adoption is necessary but not sufficient. The 29% breach rate among AI-adopting organizations reflects configuration gaps, coverage blindspots, and adversarial evasion of the same AI systems intended to provide protection. Enterprise security intelligence platforms increasingly differentiate on how deeply AI is integrated into detection logic versus how prominently it appears in marketing materials.
How Attackers Use AI Against Organizations
Offensive AI capabilities have followed the same technology curve as defensive AI, but with a critical asymmetry: attackers require only one successful technique to achieve their objective, while defenders must maintain coverage across every possible attack vector. The practical result is that AI has been adopted as aggressively by cybercriminals as by security vendors — with measurable impact on attack volume, sophistication, and success rates. The same foundation model APIs available to security researchers are available to threat actors, with specialized criminal AI toolkits available on dark web forums starting at $75.
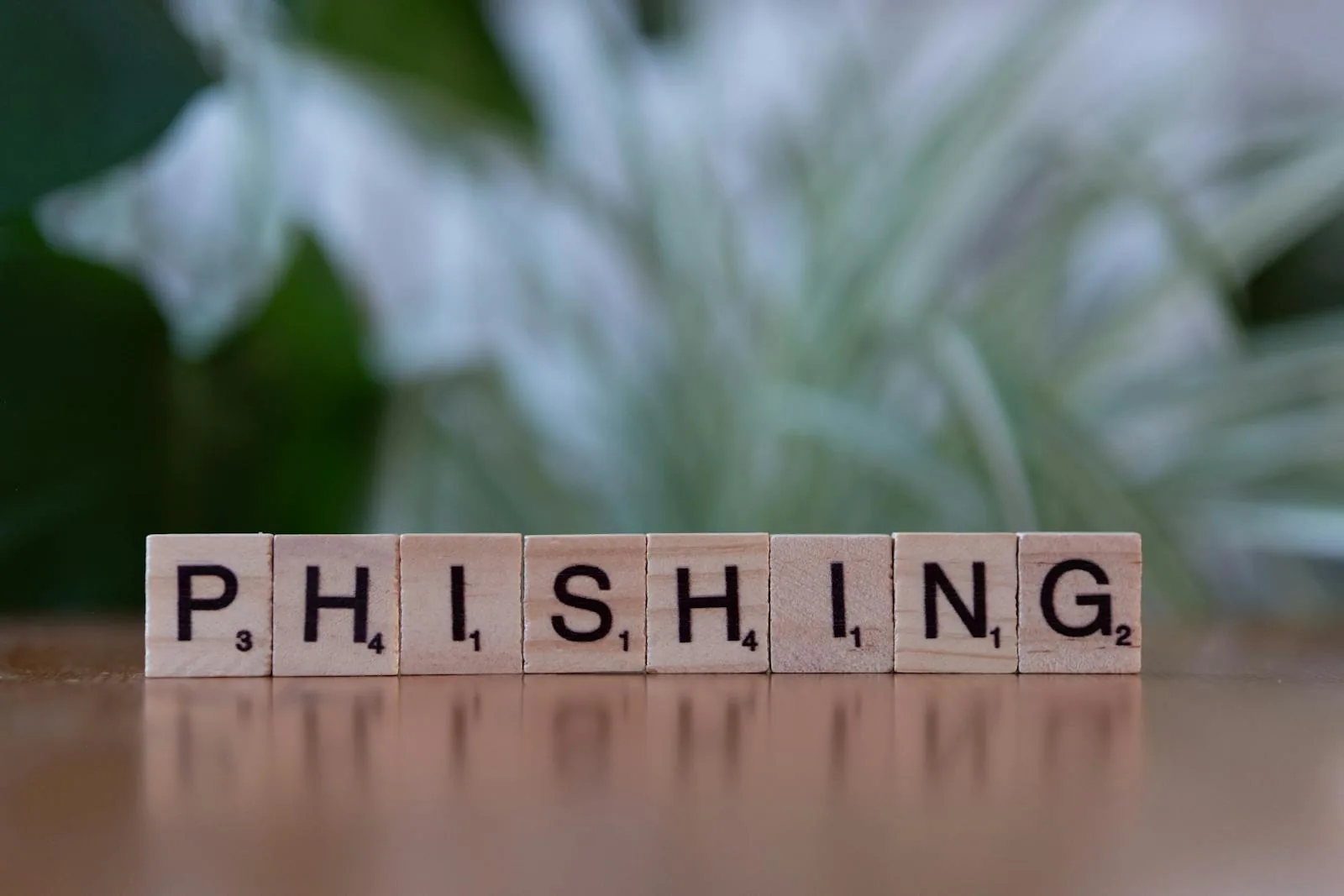
AI-Generated Phishing: Scale, Speed, and Effectiveness
AI-generated phishing represents the most immediate and widespread offensive AI application in 2026. A 1,265% surge in phishing attacks linked to generative AI has been recorded since 2023 (SlashNext research), with 82.6% of phishing emails detected between September 2024 and February 2025 using AI assistance — a 53.5% year-over-year increase. The capability shift is not just volume: AI has compressed the time to craft a convincing phishing campaign from 16 hours to roughly 5 minutes, while simultaneously improving campaign quality to the point where 68% of cyber threat analysts report AI-generated phishing is harder to detect in 2025 than in any prior year.
Effectiveness data from controlled experiments confirms the qualitative assessment: AI-crafted phishing emails achieve 54% click-through rates versus 12% for human-written equivalents — a 4.5x effectiveness gap driven by AI’s ability to personalize at scale, match organizational communication styles, exploit contextually relevant current events, and avoid common linguistic patterns that legacy email security filters detect. The economic barrier to entry has collapsed: AI-based phishing toolkits are available on criminal forums for as little as $75, meaning organizations that previously faced phishing threats primarily from sophisticated threat actor groups now face the same quality of social engineering attacks from low-skill adversaries. Threat intelligence feeds tracking active AI phishing campaigns provide early warning of new lure themes and delivery infrastructure before they reach target inboxes at scale.
Deepfakes, Ransomware, and the Broader AI Threat Landscape
Deepfake attacks have scaled from isolated proof-of-concept incidents to a statistically significant fraud vector. Deepfake incidents increased tenfold globally from 2023 to 2025, with regional concentration in North America (+1,740%), Asia-Pacific (+1,530%), and Europe (+780%). Deepfakes now account for 6.5% of all fraud attacks — a 2,137% increase since 2022 — with Q1 2025 alone recording 19% more deepfake incidents than all of 2024. In mid-2025, the FBI issued a formal warning that attackers were sending AI-generated voice messages impersonating senior U.S. government officials; voice cloning now requires as little as 30 seconds of source audio, making any public figure or executive a practical target for business email compromise and vishing campaigns.
Ransomware has adopted AI as an operational accelerator: an MIT analysis of 2,800 incidents found 80% of ransomware attacks in 2025 leveraged AI tools — primarily for target identification, spearphishing initial access, and automated lateral movement execution. Global ransomware damage costs reached $57 billion annually in 2025, while average ransom payments actually declined to $1.0 million (down 50% from $2.0 million in 2024) — reflecting improved backup and recovery capabilities at large enterprises, not reduced attack frequency. Global cybercrime damages are projected at $10.5 trillion in 2025, rising to $23 trillion by 2027 (US Deputy National Security Advisor estimate), with AI functioning as the primary capability multiplier that enables this cost trajectory. The MITRE ATLAS framework (Adversarial Threat Landscape for Artificial Intelligence Systems) provides the structured taxonomy for documenting and defending against AI-targeted attacks — including model evasion, adversarial inputs, and model supply chain compromise that are emerging as the next frontier of AI-enabled offensive capability. Threat intelligence feeds that track AI-enhanced threat actor toolkits provide the earliest available warning of which AI attack capabilities are being operationalized before they reach mainstream criminal use.
Frequently Asked Questions
How is AI used in cybersecurity threat detection?
AI is used in cybersecurity threat detection through several techniques: machine learning behavioral analytics (UEBA) that establish baselines and flag anomalous user and system behavior; LLM-integrated SIEM pipelines that apply natural language understanding to log analysis and alert triage; neural network-based endpoint detection that identifies malicious code patterns without signature matching; and agentic AI systems that execute multi-step investigation and response workflows autonomously. Platforms like CrowdStrike Charlotte AI (98% decision accuracy), Microsoft Security Copilot (6.5x faster phishing triage), and Darktrace Cyber AI Analyst (equivalent to 30 additional analysts) represent the current state of production AI-powered threat detection.
How does AI reduce the cost of data breaches?
IBM’s 2025 Cost of a Data Breach report documents that organizations with extensive AI and automation in security pay an average of $3.62 million per breach versus $5.52 million without AI — a 34% cost reduction ($1.9 million differential). The mechanisms are time compression: AI-equipped organizations identify and contain breaches in 184 days versus 264 days, an 80-day improvement that directly reduces attacker dwell time. Specific AI capabilities and their average cost contribution: AI/ML security insights ($223,503 savings per breach), security analytics and SIEM ($212,061), DevSecOps ($227,192). The cumulative effect of deploying multiple AI security capabilities accounts for the full $1.9 million differential.
How are hackers using AI to launch cyberattacks?
Attackers are using AI in three primary categories: (1) Social engineering — generative AI compresses phishing campaign creation from 16 hours to 5 minutes; AI-crafted phishing emails achieve 54% click-through rates versus 12% for human-written lures; 82.6% of phishing emails in 2025 used AI assistance. (2) Deepfakes — voice cloning from 30 seconds of source audio enables impersonation attacks; deepfake fraud incidents increased 1,740% in North America since 2022. (3) Ransomware automation — 80% of 2025 ransomware attacks leveraged AI tools for target identification, spearphishing, and automated lateral movement. AI attack toolkits are available on criminal forums starting at $75.
What is an agentic SOC in cybersecurity?
An agentic SOC (Security Operations Center) uses AI agents that act autonomously — not just assist analysts — to execute investigation and response sequences without continuous human direction. Instead of flagging an alert for analyst review, an agentic AI system investigates the alert, queries additional context from connected security tools, assesses risk, and executes containment actions (isolating an endpoint, blocking a domain, disabling a credential) based on predefined policies and AI judgment. CrowdStrike’s Charlotte AI AgentWorks (Fall 2025) and Palo Alto’s Cortex AgentiX (October 2025, trained on 1.2 billion playbook executions) represent the current commercial state of agentic SOC deployment. The model addresses the analyst shortage by having AI handle tier-1 and tier-2 response, reserving human analysts for escalations requiring judgment.
Can AI replace human cybersecurity analysts?
Current evidence suggests AI significantly augments but does not replace human analysts. CrowdStrike Charlotte AI saves analysts approximately 40 hours per week; Darktrace Cyber AI Analyst provides the equivalent of 30 additional analysts for routine investigation. But 29% of organizations that adopted AI-powered threat detection in 2025 still suffered AI-based breaches — reflecting that AI coverage has gaps requiring human judgment for novel attack techniques, adversarial evasion, and contextual decision-making in ambiguous cases. The emerging model is an agentic SOC where AI handles high-volume tier-1 detection and response autonomously, while human analysts focus on threat hunting, intelligence analysis, strategic decisions, and novel attack investigation that AI systems are not yet trained to handle.